The clock is ticking: less than 3 months until the Dutch Cybersecurity Act
The Cyberbeveiligingswet — the Dutch implementation of the European NIS2 directive — is expected to take effect on July 1, 2026. The Dutch parliament is processing the bill in spring 2026 and the government is committed to a Q2 2026 implementation date.
For thousands of Dutch organizations, this means the time to act is truly running out. Most companies need four to six months to bring their cybersecurity to the required level. Those who haven't started yet face a serious risk of non-compliance.
In this article, we cover everything: does your organization fall under the act, what are the obligations, and what should you tackle this month?
Does your organization fall under the Cybersecurity Act?
The act distinguishes between two categories of organizations, each with its own supervisory regime:
Essential entities (proactive supervision)
Organizations of major societal importance in sectors such as:
Essential entities undergo proactive supervision: regulators actively check whether you meet the obligations.
Important entities (reactive supervision)
Organizations in sectors such as:
Important entities undergo reactive supervision: checks mainly take place after incidents or based on non-compliance signals.
Size criteria
You fall under the act if your organization operates in one of the above sectors and meets these criteria:
| Type | Employees | Annual turnover | Balance sheet total |
|---|---|---|---|
| Medium-sized | 50–250 | €10–50 million | €10–43 million |
| Large | >250 | >€50 million | >€43 million |
Note: Certain organizations always fall under the act, regardless of size. This applies to providers of public electronic communications networks, qualified trust service providers, and government organizations.
Even if your organization doesn't directly fall under the act, you may be indirectly affected as a supplier to organizations that do.
The four pillars of the Cybersecurity Act
The act has four main obligations:
1. Duty of care: the 10 mandatory measures
The core of the act: your organization must take appropriate and proportionate technical, operational and organizational measures. The act prescribes ten specific measure areas:
| # | Measure | What it involves |
|---|---|---|
| 1 | Risk analysis | Map vulnerabilities and threats, determine priorities |
| 2 | Access management and personnel | Control who has access to which systems, register hardware and software |
| 3 | Business continuity | Create a BCP so you can continue operating during disruptions |
| 4 | Incident response | Set up a structured Incident Response Plan for rapid action during incidents |
| 5 | Cyber hygiene | Strong passwords, timely updates, security awareness among employees |
| 6 | Network and information security | Protect your technical infrastructure against attacks |
| 7 | Supply chain security | Assess and monitor the security of your suppliers |
| 8 | Cryptography and encryption | Establish policies for encryption, key management and certificates |
| 9 | Multi-factor authentication | Secure access with MFA and secure authentication methods |
| 10 | Evaluation and improvement | Regularly measure the effectiveness of your measures and continuously improve |
These ten measures are not optional — they constitute the legal minimum. Your organization must be able to demonstrate they are implemented.
2. Reporting obligation: the three-step protocol
In the event of a significant cyber incident, you must report to the NCSC through their reporting portal. This follows three steps:
| Step | Deadline | What to report |
|---|---|---|
| Early warning | Within 24 hours | Initial detection: what happened? Is there a suspected attack? |
| Follow-up report | Within 72 hours | Additional information: scope, impact, initial severity assessment |
| Final report | Within 1 month | Detailed analysis: root cause, measures taken, lessons learned |
The NCSC portal automatically forwards your report to both the CSIRT and the supervisory authority, preventing duplicate reporting.
3. Registration obligation
Organizations covered by the act must register with the NCSC. You provide information such as name, sector, contact details, and IP ranges. Registration must take place before a specified date after the act enters into force.
4. Board liability
This is new and significant: board members are personally responsible for cybersecurity compliance. Specifically:
This is comparable to GDPR accountability, but now specifically for cybersecurity. Board members who simply delegate cybersecurity without oversight are at risk.
Fines: comparable to GDPR
Sanctions are substantial and depend on your classification:
| Classification | Maximum fine |
|---|---|
| Essential entities | Up to €10 million or 2% of global annual turnover |
| Important entities | Up to €7 million or 1.4% of global annual turnover |
The higher amount of the two applies. For an organization with €500 million turnover, the fine could reach €10 million.
Practical checklist: what to do now?
With less than 3 months until the expected entry into force, there's no time to lose. Here's your action plan for the coming weeks:
Weeks 1-2: Determine your status
Weeks 3-4: Gap analysis
Weeks 5-8: Implement core measures
Weeks 9-12: Consolidation and registration
The relationship with ISO 27001
Good news if you're already ISO 27001 certified: there is significant overlap with the Cybersecurity Act. Many of the 10 duty-of-care measures align with what you have already arranged within your ISMS — think of risk analysis, access management, incident response, business continuity and cryptography.
However: ISO 27001 alone is not sufficient for full compliance. The Cybersecurity Act imposes additional requirements, particularly around:
Integrating NIS2 requirements into your existing ISMS is the most efficient approach. This prevents duplicate work and builds on what's already in place.
How uComply helps with the Cybersecurity Act
uComply is designed to help organizations set up and maintain a compliance management system — including for the Cybersecurity Act.
NIS2/Cbw Content Pack
The NIS2 Content Pack in uComply includes:
Multi-standard integration
Already ISO 27001 certified? uComply automatically links overlapping controls. One measure you document for ISO 27001 immediately counts for the Cybersecurity Act. This saves up to 40% implementation time.
Board reporting
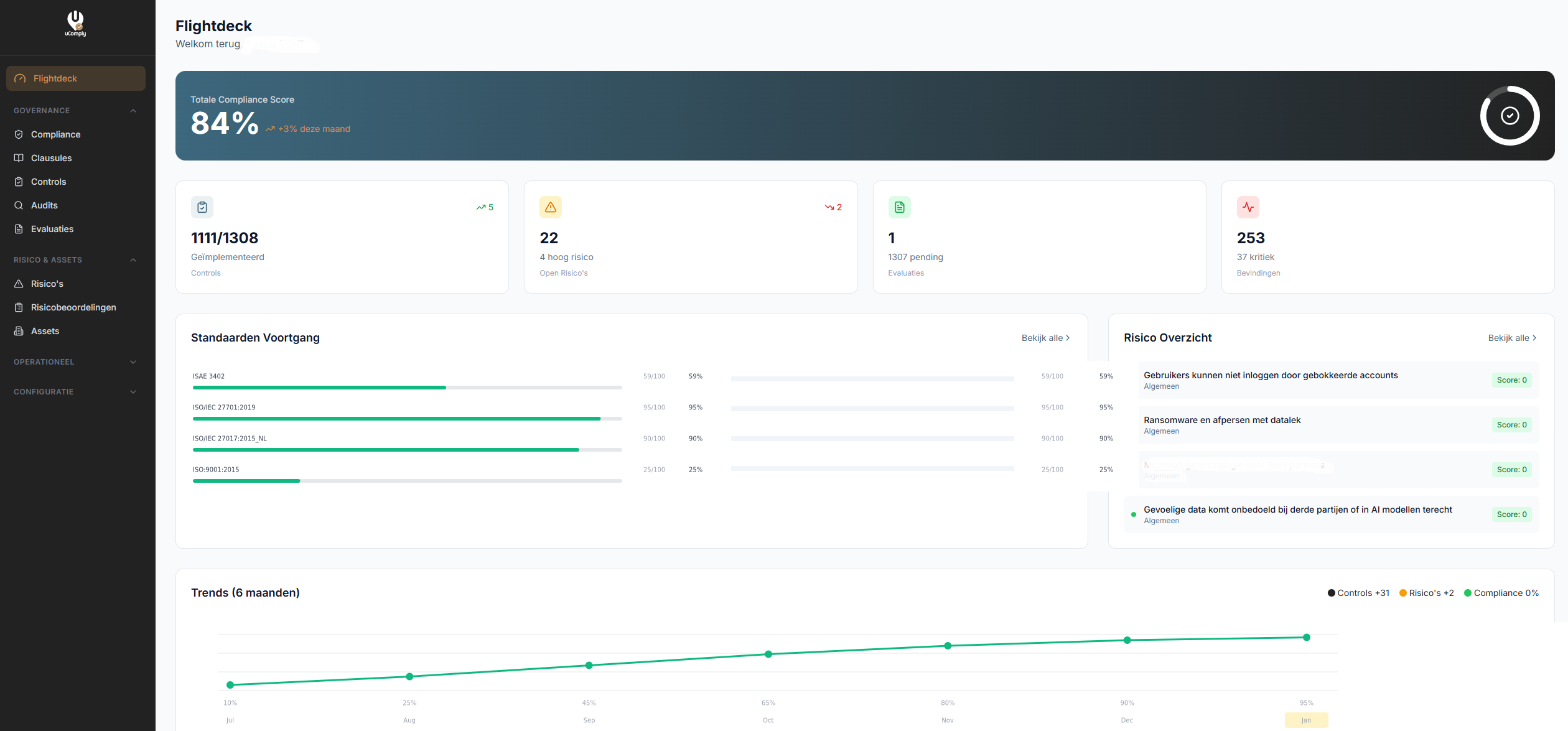
With the Flightdeck dashboard, you give board members real-time insight into compliance status — exactly what they need to give well-considered approval and meet the training obligation.
AI support
The uComply AI Consultant helps interpret duty-of-care measures, draft policies, and answer questions about the Cybersecurity Act — available 24/7.
Conclusion: starting now is the only option
The Cybersecurity Act is no longer a future concern. With the expected entry into force on July 1, 2026, organizations have less than three months to become compliant. The combination of duty of care, reporting obligations, registration requirements, and personal board liability makes this an act you cannot ignore.
Fines are comparable to GDPR, but the impact of non-compliance goes further: cyber incidents affect your business continuity, reputation, and customer relationships. Investing in cybersecurity is not just a legal obligation, it's a business-critical necessity.
Start today. Schedule a demo and discover how uComply helps you comply with the Cybersecurity Act on time.
Frequently Asked Questions
When does the Cybersecurity Act take effect?
The expected entry into force is July 1, 2026. The bill was submitted to parliament in June 2025 and is being processed in spring 2026.
Is the Cybersecurity Act the same as NIS2?
The Cyberbeveiligingswet is the Dutch implementation of the European NIS2 directive. The core is the same, but the Dutch act contains specific implementations for supervision, reporting procedures, and board obligations.
Does the act apply to SMEs?
If your organization operates in one of the designated sectors and has at least 50 employees or annual turnover above €10 million, you likely fall under the act. Use the self-assessment tool at ncsc.nl to be certain.
What if I'm already ISO 27001 certified?
ISO 27001 provides a strong foundation, but is not sufficient for full compliance. You must additionally arrange the reporting obligation, registration requirement, and board liability. uComply helps integrate both standards.
Can board members really be held personally liable?
Yes. The Cybersecurity Act contains an explicit provision on board liability. Board members must approve measures, oversee implementation, and have sufficient cybersecurity knowledge.